CryptoWall is back with an improved version number 3.0 implemented to cause more havoc.
CryptoWall 3.0 was discovered in January 2015 by Heimdal Security firm. The ransomware basically has the same capabilities as CryptoLocker and the previous version of CryptoWall but with improved capabilities to hide from being detected and increase anonymity by using the TOR network for transmission of data.
The ransomware is still delivered through mass mail blasts and compromised websites. Around 45 compromised websites are used as the delivery platform for the ransomware once a user downloads the original .chm file from their email or infected websites.
Once the target computer is compromised, it is redirected to a webpage hosted to Google Drive where the malware is downloaded and automatically installed on the victim’s computer.
The malware then uses an exploit kit found in most computers to look for vulnerabilities in common programs such as Microsoft Word, Excel, Adobe Flash, Java and more.
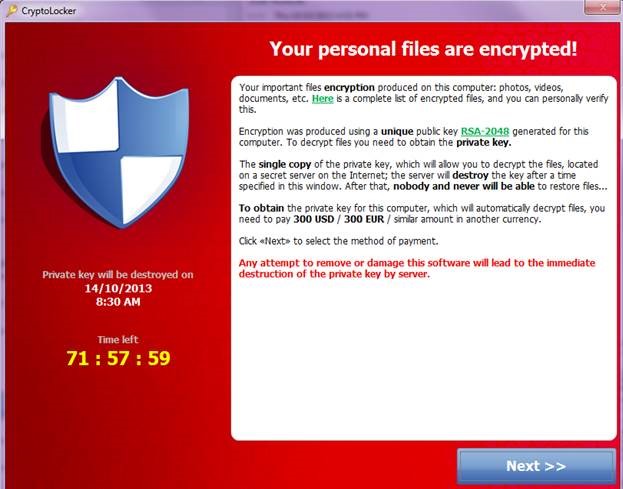
The malware then starts encrypting common files on the computer and deletes the original files. Once the encryption process is completed the victim is presented with a message to pay the ransomware, which can range from $100 to $10,000+.
How can you reduce the risk of being infected by CryptoWall 3.0?
- Make sure you have a backup policy in place to enable you to recover from data loss. Always backup and keep the backup copy outside your network to prevent the backup file from being infected.
- Do not browse unsafe websites. Most anti-virus programs will warn you about unsafe websites.
- Keep your anti-virus up-to-date and run regular scans of your computer and server.
What can I do you do if your computer is infected?
- If you believe your computer might have been affected by the malware, it is recommended to run your anti-virus scan.
- Seek professional advice, which Forerunner’s Technicians can help you with.
- If you have been presented with a payment it most probably means that the malware has finished encrypting all your files.
If you are infected and you decide to pay the ransom, there is no guarantee that after paying the ransom that you will recover your files, that your computer will be ‘clean’ or not be re-infected.
Contact us today if you have any questions or suspect you have been infected, on 8269 5260.