Beware of CryptoLocker Ransomware Trojan
Computers all over the world are being infected with ransonware and unfortunately you could be next. CryptoLocker is one of the newest ransomware causing mayhem. It is one of the nastiest malwares we have ever seen.
The creators of CryptoLocker Ransomware are getting smarter and sneakier. Once you have been infected, your documents becomes unusable as they have been encrypted using asymmetric encryption which requires you to have a private and a public key. If you are asking if this happens to you, how do you get your data back, it is simple… pay the ransom which is currently being set at $US300 or say goodbye to your data forever. However we discourage you from paying in doing so you would help these scammers from to attack more people.
Below is an image from Microsoft on how the encryption technique works.
Some common files which are targeted by Cryptolocker Ransomware
The list keeps increasing as the scammer keeps on updating the Trojan.
doc, docx, xls, xlsx, ppt, pptx, mdb, rtf,psd, pdd, jpg, srf, erf, mef, mrw, nef, nrw, raf, raw, rwl, rw2, ptx, pef, srw, x3f, der, cer, crt, pem & counting..!
Whether you choose to pay the ransom or not, there is never going to be a 100% guarantee that you are going to get your data back. And if you do, there are possibly going to still be traces of ransomware, or something else, on your computer, so you should back up and format your computer and rebuild just to be sure.
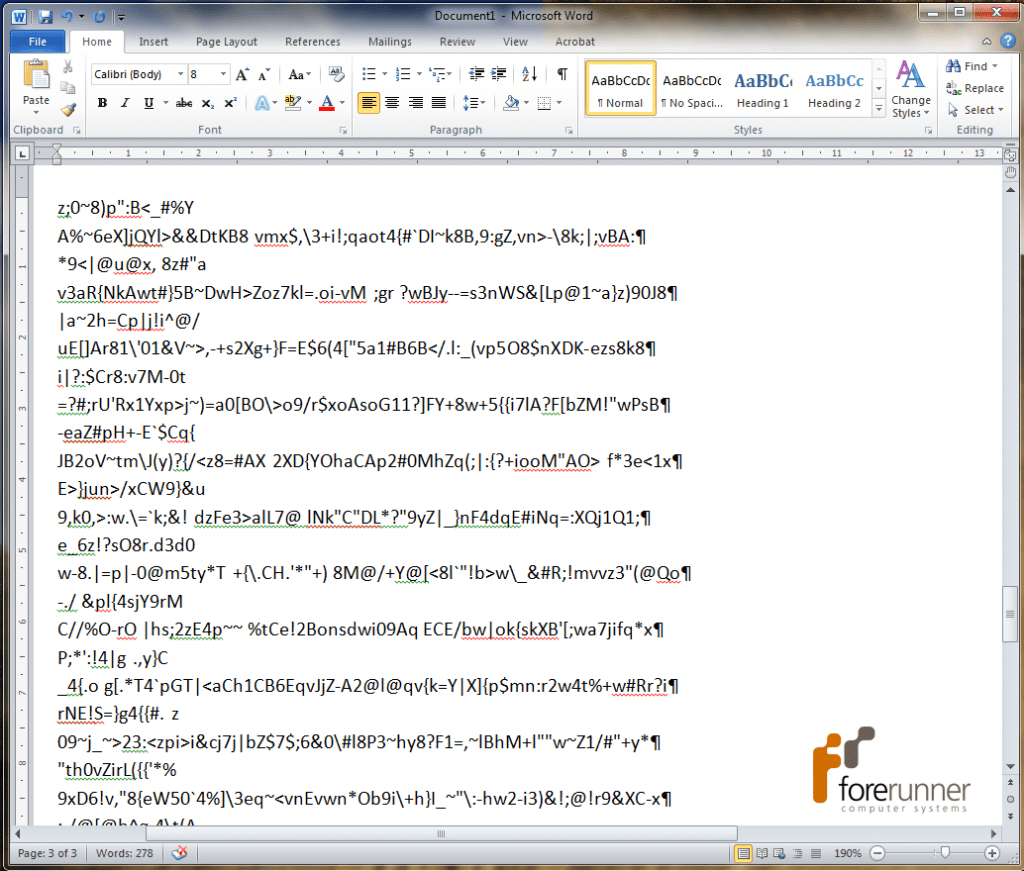
What does an infected file looks like? – We have mockup one for our readers below!
When you try to open a document infected by CrytoLocker it will contain symbols and characters which are unreadable and usually this can be seen in doc, docx, text files.
It is as simple as opening an email with an attachment from someone you do not know and triggering the virus. Opening an attachment from someone you do not know and that you’re not expecting is just asking for trouble. If this happens to you, our word of advice is to contact the sender to see if it is legitimate or simply find the DELETE key on your keyboard. It is important to practice ‘safe emailing’. Do not let curiosity get the better of you. If you are not specifically expecting an email with a zip or exe attachment, then just delete it. You can always call the sender if they are legitimate and ask them to re-send if necessary.
Do not be tempted to click on any links supplied in emails which request you to confirm any of your account or personal details. The website that you are redirected is likely to be infected.
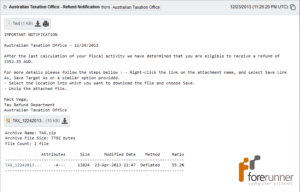
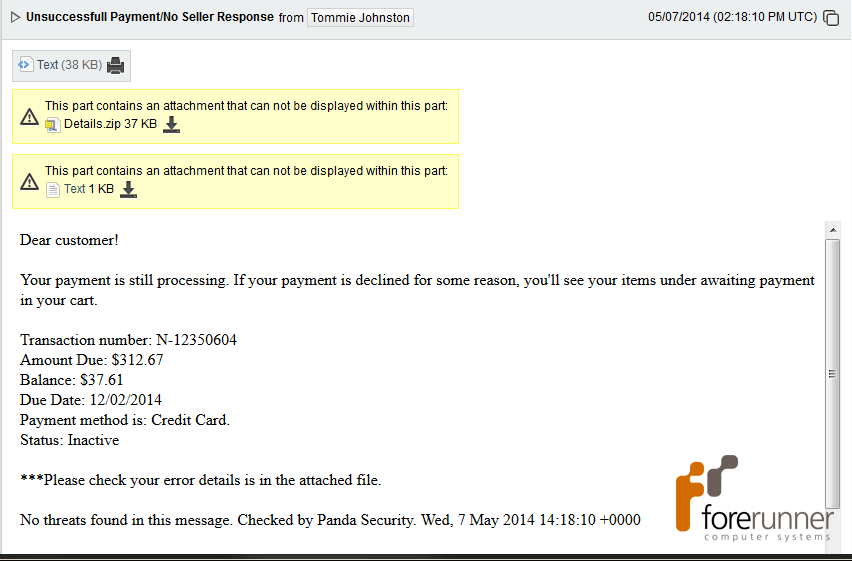
What does a cyptolocker infected email look like? These are real emails received in spam filters!
Notice the attachment in both emails and the scammer is using social engineering to get your details and make you open the attachment.
It is important to make sure that your anti-virus is up-to-date, but even then there is no guarantee that your computer is safe. Regularly backing up your data onto another device, external hard drive, server or in the cloud is very important. It appears this virus can spread to shared network drives, therefore it is important to regularly swap over your backup drives is essential to ensure that your backups cannot be infected with this virus as well.